No. It is an add-on to LogRhythm SIEM.
ADD ADVANCED DETECTION TO LOGRHYTHM SIEM
Know What Your Data Is Telling You
Transform your SIEM with AI-driven insight. Ingest logs, alerts, and telemetry, enrich them with context, and run detections that reveal activity point tools miss.
INTEGRATED USER EXPERIENCE
Stay in the LogRhythm Interface
Add AI-powered detections for insider threats and compromised accounts without leaving your SIEM workflow. Findings appear in case management on day one through LogRhythm Log Distribution Service.
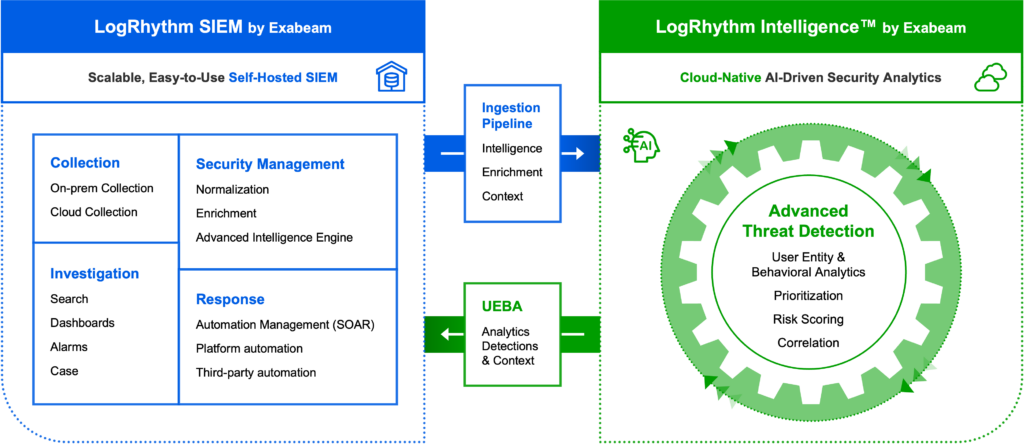
How it Works
LogRhythm Intelligence applies behavioral analytics models to LogRhythm SIEM data and delivers detections into your existing workflow. Build dashboards, run searches, set alarms, and automate actions as you do with any log source. These detections help your security operations team identify insider threats, credential misuse, privilege abuse, and identity-driven attacks. Exabeam Nova summarizes findings and guides analysts to next steps.

How can we help? Talk to an expert.
Contact UsFrequently Asked Questions
Is LogRhythm Intelligence available as a standalone product?
Is LogRhythm Intelligence self hosted?
No. It uses New-Scale Fusion to create a hybrid LogRhythm SIEM deployment.
What is the pricing of LogRhythm Intelligence?
Contact your sales representative.
How long does deployment take?
It is added as a data source. Deployment time matches adding any new data source.
Does LogRhythm Intelligence give me better detection capabilities?
Yes. Behavioral analytics gives you deeper insight into user and entity activity and expands uses cases such as insider threats.
“In the modern security landscape, the regular release of innovative products and AI tools ensures we have the necessary solutions to strengthen our defenses and respond to threats with speed and accuracy… Exabeam is a key part of our security strategy.”
See Exabeam in Action
Request a demo to see how Exabeam helps security operations teams secure the agentic enterprise.
You’ll learn how to:
- Monitor and analyze human & agent behavior to uncover risk
- Investigate threats with machine-built timelines
- Use multi-agent AI to improve detection, investigation, and response workflows
- Apply playbooks to guide decisions
- Support compliance requirements
Award-Winning Leader in Security


































